How Does Facial Recognition Access Control Improve Enterprise Security
In many enterprise environments, access control is still managed using cards or PIN codes — systems that are easy to lose, share, or misuse.
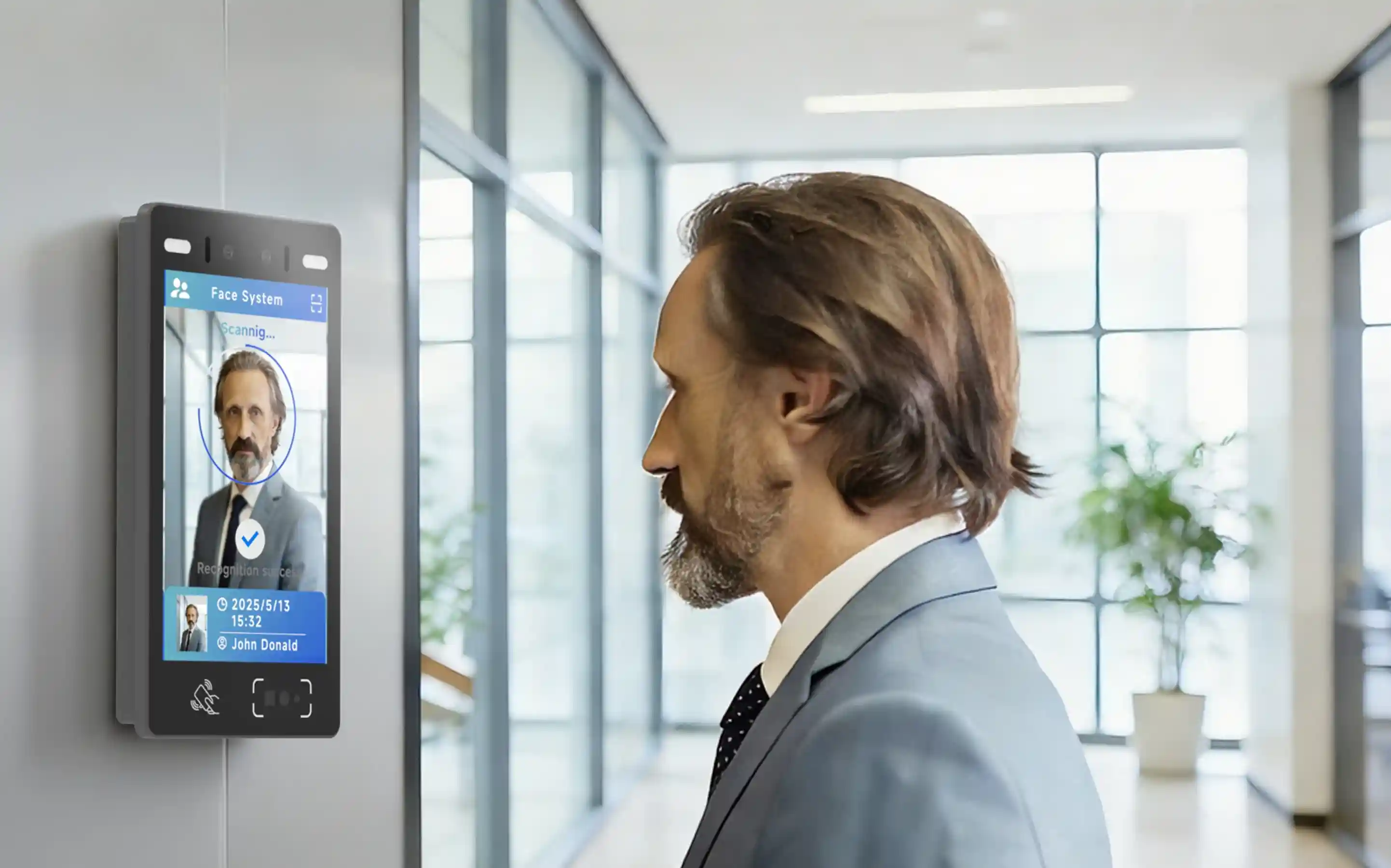
Facial recognition access control changes this by turning a person’s face into a secure and contactless credential. Instead of carrying cards or remembering passwords, employees can be verified instantly as they approach an access point.
For organizations managing hundreds or thousands of employees, this shift is not just about convenience — it directly impacts security, operational efficiency, and long-term cost.
Facial recognition access control is now widely adopted across global markets, including office environments, commercial buildings, and high-security facilities in regions such as Europe, the Middle East, and Latin America.
What Is Facial Recognition Access Control?
Facial recognition access control is a type of biometric access control system that identifies individuals based on unique facial features.
How Does Facial Recognition Access Control Work?
A typical system works through several steps:
- A camera captures the user’s face
- AI algorithms extract key facial features
- The system compares the data with a stored database
- Access is granted or denied within milliseconds
Unlike traditional systems, there is no need for physical credentials. This reduces the risk of loss, duplication, or unauthorized sharing.
Enterprise-grade devices such as FA5 further enhance this process by combining AI processing capabilities with stable commercial hardware, ensuring fast and reliable recognition in real-world environments.
Where Is Facial Recognition Access Control Used in Enterprises?
How Does Facial Recognition Improve Office Entry Efficiency?
Core Pain Point
Facial recognition access control systems are widely deployed across different enterprise environments depending on security requirements and operational needs.
At office entrances and building entry points, access control systems must handle a high volume of people within a short period of time, especially during peak hours such as morning arrivals or shift changes.
Traditional methods such as card swiping or PIN entry often create bottlenecks. Employees need to stop, present credentials, or manually interact with devices, which slows down entry and leads to congestion. In larger office buildings, this can significantly impact daily operations and employee experience.
Facial recognition access control enables a more seamless flow by allowing users to be verified as they approach the entrance. Instead of stopping to authenticate, employees can pass through access points naturally, with identity verification happening in real time.
Modern systems are designed to maintain both speed and accuracy, even in dynamic environments with varying lighting conditions and high traffic. This ensures consistent performance throughout the day without compromising security.
In addition, facial recognition access control can support multiple user types, including employees, visitors, and contractors. Temporary access can be managed through QR codes or mobile credentials, while employees benefit from frictionless entry using facial authentication.
Business Value
Deploying facial recognition access control at office entrances provides measurable operational benefits:
- Reduced congestion during peak hours and smoother entry flow
- Improved user experience with faster, contactless access
- Lower dependency on physical credentials such as cards
- More efficient management of visitor and employee access
For enterprises with large workforces or multi-tenant office buildings, optimizing entry points is one of the most impactful ways to improve daily operational efficiency.
Explore FA5 for office access control →
How Can Facial Recognition Improve Meeting Room Management?
Core Pain Point
In many enterprises, meeting rooms are managed through digital booking systems, but access control is often disconnected from actual usage. Rooms may be reserved but left unused, occupied without proper booking, or accessed by unauthorized personnel.
This creates several operational challenges:
- Meeting spaces are underutilized despite high demand
- Scheduling conflicts increase due to inaccurate room availability
- Meetings may be interrupted by unexpected access
These issues are especially common in large organizations where meeting frequency is high and centralized coordination becomes difficult.
Facial recognition access control systems can address this by linking identity verification directly with meeting room booking platforms. When a user approaches the meeting room entrance, the system checks their reservation status in real time and grants access only to authorized participants.
In addition, modern facial recognition terminals support multiple access methods, including:
- Facial authentication for employees
- QR code access for temporary visitors
- Mobile-based credentials where applicable
This allows organizations to manage both internal and external participants without compromising security or user experience.
Many enterprise-grade devices also include integrated displays that show real-time room status such as “In Meeting” or “Available,” eliminating the need for manual updates and reducing administrative workload.
Business Value
Implementing facial recognition access control for meeting rooms enables enterprises to move from manual coordination to a more automated and data-driven approach.
Key benefits include:
- Improved meeting room utilization through accurate access control
- Reduced administrative effort in managing bookings and access permissions
- Lower operational costs by minimizing wasted space and inefficiencies
- Enhanced workplace experience with fewer interruptions and clearer room status
With relatively low investment in smart access control hardware, organizations can significantly improve how meeting spaces are managed. This makes meeting room access control one of the most practical and fastest-return use cases for facial recognition in enterprise environments.
See how FA5 supports smart meeting room access →
How Does Facial Recognition Protect High-Security Areas?
Core Pain Point
In high-security enterprise environments such as R&D centers, finance departments, server rooms, and critical warehousing areas, access control is directly linked to business continuity and data protection.
Traditional card-based systems present clear vulnerabilities. Access cards can be lost, shared, or misused, making it difficult to ensure that only authorized personnel enter sensitive areas. In environments where intellectual property, financial data, or critical infrastructure is involved, these risks are often unacceptable.
Facial recognition access control addresses these challenges by binding access permissions directly to an individual’s identity rather than a transferable credential.
Modern enterprise-grade systems typically include:
- AI-based liveness detection to prevent spoofing attempts using photos or videos
- Multi-factor authentication options, such as facial recognition combined with RFID cards or PIN codes
- Real-time access logging for audit and compliance purposes
This allows organizations to implement layered security strategies based on the sensitivity of each area. For example, general staff access may require only facial authentication, while restricted zones can enforce dual-factor verification.
In addition, facial recognition systems generate detailed and traceable access records, which support internal audits and compliance requirements. In regions with strict data protection frameworks, such as those governed by the General Data Protection Regulation, this level of traceability is particularly important.
Business Value
Implementing facial recognition access control in high-security environments enables enterprises to move from credential-based security to identity-based security.
Key benefits include:
- Reduced risk of credential sharing, loss, or unauthorized access
- Stronger protection for sensitive assets and critical infrastructure
- Improved compliance with internal governance and regulatory requirements
- Clear audit trails for accountability and incident investigation
With modern facial recognition systems capable of fast and accurate identity verification, organizations can maintain high security standards without compromising operational efficiency.
This makes high-security access control one of the most critical and high-value use cases for facial recognition in enterprise environments.
How Does Facial Recognition Improve Security for Executive Offices and Restricted Zones?
Core Pain Point
In executive offices and VIP areas, access control is not only about security, but also about user experience and corporate image.
Traditional methods such as card swiping or manual registration often create friction. Cards can be forgotten, lost, or shared, while manual processes interrupt the flow of movement and introduce unnecessary delays. In high-level office environments, these limitations are increasingly seen as outdated.
Facial recognition access control provides a more seamless and modern approach by allowing authorized personnel to enter without physical credentials. Users can simply approach the entrance and be verified instantly, creating a smooth and uninterrupted access experience.
In addition to convenience, these systems are designed to meet higher expectations for accuracy and reliability, ensuring that only authorized individuals can enter sensitive executive areas.
Modern facial recognition terminals also support flexible deployment strategies, including privacy-focused configurations and secure data handling practices aligned with frameworks such as the General Data Protection Regulation.
From a design perspective, many enterprise-grade devices are built to integrate naturally into premium office environments, with compact form factors and refined aesthetics that align with modern workspace design.
Business Value
Implementing facial recognition access control in executive and VIP areas provides both operational and strategic benefits:
- Stronger protection for confidential business discussions and sensitive information
- Reduced risk of unauthorized access caused by lost or shared credentials
- Improved user experience for executives and senior staff
- Reinforcement of a modern, technology-driven corporate image
By combining security, convenience, and design, facial recognition access control becomes more than just a security solution — it also contributes to the overall upgrade of the workplace environment.
What Are the Key Benefits of Facial Recognition Access Control?
After understanding the different use cases, the next question for most organizations is whether facial recognition access control is worth the investment.
Compared with traditional access methods, the benefits are not limited to convenience — they directly impact operational efficiency, security, and long-term cost.
Faster and Truly Contactless Access
Unlike card-based or PIN-based systems, facial recognition allows users to be authenticated without any physical interaction.
This becomes particularly important in high-traffic environments such as office entrances or shared workspaces, where even small delays can create noticeable congestion. Users can simply walk into the recognition area, where identification and verification are performed automatically. There is no need to stop to enter a password or present a card, which improves passage efficiency and reduces the risks of credential misuse.
Over time, this reduction in friction leads to smoother daily operations and a better overall workplace experience.
Stronger Security Based on Identity, Not Credentials
Traditional systems rely on something a user has (card) or knows (PIN). These can be lost, shared, or misused.
Facial recognition shifts access control to something a user is, making it significantly harder to bypass. A face terminal verifies users by conducting liveness detection and matching their biometric data. This includes both 1:1 verification and 1:N matching. In other words, a face terminal helps answer “Who are you?” and “Are you really who you claim to be?” which maximizes security and minimizes unauthorized access.
Modern systems also include anti-spoofing technologies. According to CyberLink, advanced facial recognition systems can achieve high accuracy when combined with liveness detection.
Lower Operational Overhead Over Time
While facial recognition systems may require higher initial investment, they reduce ongoing operational costs:
- No need to issue or replace access cards
- Fewer administrative tasks related to access management
- Reduced risk of security incidents caused by credential misuse
For medium to large enterprises, these savings become more significant over time. Moreover, face recognition terminals deliver substantial value in improving enterprise operational efficiency by reducing labor input and minimizing errors.
Scalable Integration with Enterprise Systems
Facial recognition access control can be integrated with:
- HR and attendance systems
- Visitor management platforms
- Building management systems
- Meeting booking systems
- Member management systems
This allows organizations to build a more connected and automated operational environment.
Facial Recognition Access Control vs Traditional Access Control Methods
When evaluating different solutions, it is important to understand how facial recognition compares with traditional systems.
| Feature | Facial Recognition | RFID Card | PIN Code |
|---|---|---|---|
| Security | High | Medium | Low |
| Convenience | High | Medium | Low |
| Contactless | Yes | No | No |
| Risk of Loss | None | High | Medium |
In practice, many organizations adopt a hybrid approach, using facial recognition as the primary method while keeping cards or PINs as backup options for specific scenarios.
How to Choose a Facial Recognition Access Control System
Selecting the right system depends on how it will be used in your environment.
A small office with a single entry point has very different requirements compared to a large enterprise with multiple buildings and security zones.
Evaluate Your Access Scenarios
Start by identifying where the system will be used:
- Office entrances
- Meeting rooms
- High-security areas
- Attendance tracking
Different scenarios may require different configurations. For places such as offices, enterprise gates, and building entrances with heavy foot traffic and high passage frequency, as well as complex lighting conditions and identity verification across diverse user groups, higher-spec configurations may be required for cameras, recognition algorithms, storage, and long-term hardware stability. Attendance management also has high requirements for accuracy and reliable data storage for later verification and inspection.
Define Security Levels
Not all areas require the same level of protection.
- General office areas → facial recognition only
- Sensitive zones → multi-factor authentication
Consider Integration Requirements
Many organizations need access control systems to work with existing platforms.
Look for systems that support integration with:
- HR systems
- Scheduling platforms
- Visitor management tools
Assess Long-Term Scalability
As organizations grow, access control systems need to scale accordingly.
Choosing a system that supports centralized management and future expansion can reduce long-term costs and complexity.
Data Privacy and GDPR Considerations
When deploying facial recognition access control systems, data privacy must be carefully considered.
In regions with strict regulations, such as those governed by the General Data Protection Regulation, organizations are required to:
- Obtain user consent
- Store biometric data securely
- Ensure transparency in data usage
Even in regions without strict regulation, following these practices helps build trust and reduce potential risks.
When Is Facial Recognition Access Control Not the Best Option?
Although facial recognition offers many advantages, it is not suitable for every scenario.
For example:
- Environments with strict privacy restrictions
- Very low-budget deployments
- Locations with extremely challenging lighting conditions
In such cases, a hybrid approach combining facial recognition with other methods may be more practical.
Why Are Enterprises Adopting Facial Recognition Access Control?
As a secure and contactless biometric technology, facial recognition delivers exceptional accuracy, remarkable efficiency, and a truly seamless experience. It is widely recognized as one of the most advanced and future-oriented solutions for modern identity verification.
The adoption of facial recognition access control continues to grow as organizations seek to modernize their infrastructure.
It strikes a balance between security, convenience, and scalability, making it a practical choice for a wide range of enterprise environments.
Conclusion
Facial recognition access control is no longer a niche technology. It has become a practical and scalable solution for managing access across modern enterprises.
From meeting rooms and office entrances to high-security areas, it provides a unified approach to improving both security and operational efficiency.
Recommended Device for Enterprise Access Control
For enterprises looking to deploy a reliable facial recognition access control system, choosing the right hardware is critical.
The FA5 facial recognition terminal is designed for commercial environments, offering:
- High-speed facial recognition with AI-powered processing
- Stable performance in high-traffic scenarios
- Support for multi-factor authentication (Face + RFID + PIN)
- Integration with access control and attendance systems
- GDPR-oriented data handling capabilities
Whether used in office entrances, meeting rooms, or high-security areas, FA5 provides a scalable and enterprise-ready solution.
Explore SUNTEK FA Series Facial Recognition Terminals
The SUNTEK FA Series delivers a complete lineup of facial recognition terminals spanning 5-inch (FA5), 8-inch (FA8), and 10-inch (FA10) touchscreen models with flexible high-performance configurations.
Engineered with dual-lens (RGB+IR) liveness detection, industry-leading accuracy (>99.99%), and sub-0.2s recognition speed, these terminals are built for both indoor and outdoor environments with robust IP65 protection and high-brightness displays.
Covering the full spectrum of mainstream market scenarios — including access control, time attendance, visitor management, transportation, and smart buildings — the FA Series supports multi-modal verification (face, QR code, NFC/IC card, and mobile app) to meet diverse project demands.
Backed by SUNTEK’s experienced technical team, we provide end-to-end development and support services from pre-sales consultation and customized solutions to on-site deployment and after-sales maintenance, ensuring reliable, long-term project success.
Contact Us to Get:
- Free consultation
- Product demo
- Custom deployment solutions
We can also provide sample units and customization if needed.